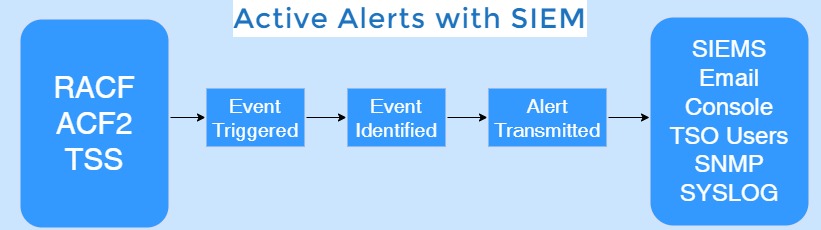
Vanguard Active Alerts sends user-specified event driven data to SIEMs, SNMP or SYSLOGD in industry standard formats as requested by the user. VAA sends event driven data to identified target devices, which receives the “real time” information in a timely manner for Compliance, Security and Audit requirements.
The SIEM requirement is driven by customer needs to apply security analytics to event data in real time for the early detection of targeted attacks and data breaches and to collect, store, analyze, and report on log data for incident response, forensics and regulatory compliance.
Vanguard’s Active Alerts provides the ability to continuously monitor security related events at the system and or user-specified level. When an event occurs, Vanguard Active Alerts will notify the SIEM in order for enterprises to take decisive action and make critical business decisions.
The SIEM provides a holistic, unified view into not only the infrastructure but also workflow, compliance and log management. SIEM can provide a multitude of capabilities and services efficiently.
At the core, SIEM provides Data Aggregation, Correlation, Alerting, Dashboards, Compliance, Retention, and Forensic Analysis.