Vanguard has a strong track record of safeguarding critical infrastructure when hardened solutions are deployed, which numerous global Fortune 100 organizations have adopted.
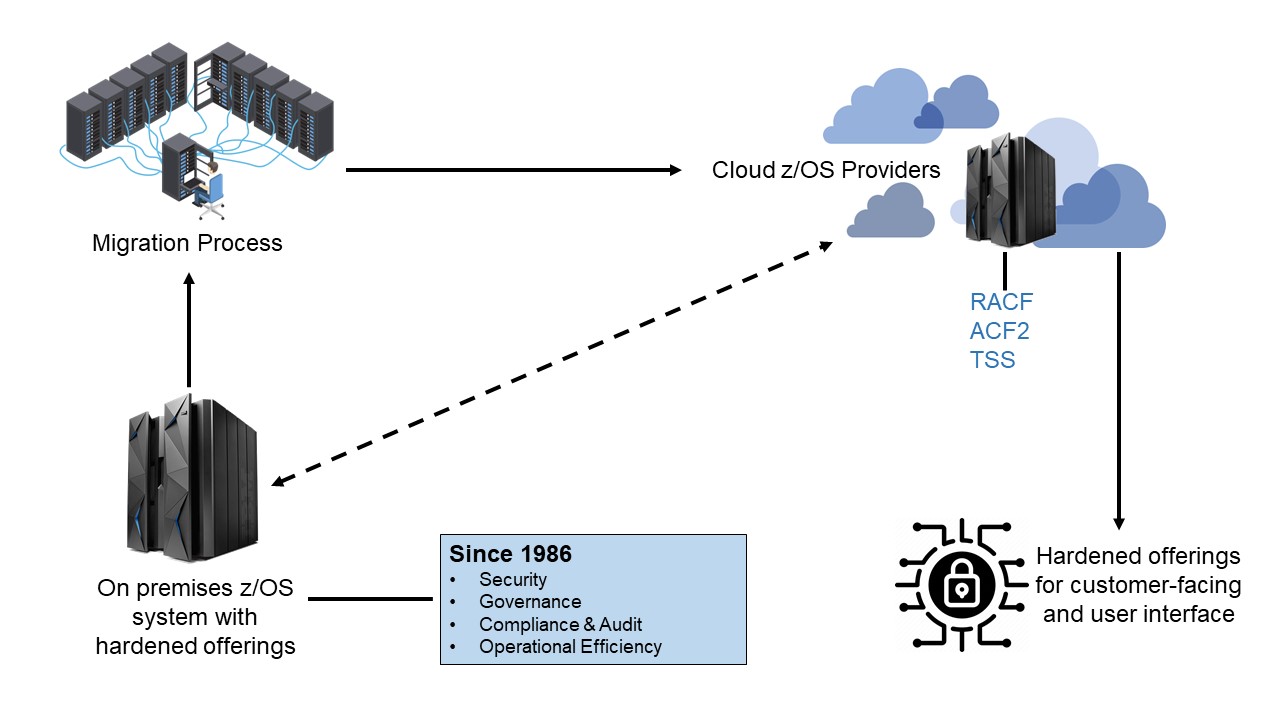
Many large enterprises are looking for ways to deploy both on-site and cloud-based solutions that leverage Vanguard’s stack of security product offerings. These tools are frequently deployed with z/Cloud providers by LPAR for RACF, ACF2 and TSS external security managers.
Securing the z/OS environment and related external security managers is a critical requirement for making cloud outsourcing migration a success. This ensures that security exposures do not increase.
While cloud-based services provide many benefits, they can also significantly increase an organization’s security risks and vulnerabilities, especially if the proper processes to safeguard corporate data are not implemented.
Vanguard has a long history of protecting the critical infrastructure when hardened solutions are deployed and utilized like many of the world-wide Fortune 100 organizations have leveraged.
Vanguard works closely with organizations that currently deploy z/Cloud Services for targeted mainframe modernization programs during the journey to cloud services.
During this journey, organizations are still required to meet the strict requirements of governance, risk and compliance. In an ever-changing world of strict regulations and reporting, the market demands improved operational efficiency, a reduced amount of human intervention, and the use of real-time accurate information. This produces instantaneous statuses for critical applications in the z/OS environment and beyond.
Historically, the mainframe has provided shared computing resources (known today as cloud computing) to enterprise customers for more than four decades. These services, previously known as timeshare services or data service vendors, provide companies with a shared pool of computing resources that are managed centrally and deliver on-demand user access to applications and services.
To minimize risk, enterprises using cloud computing must ensure that their systems are secure and that control is centrally managed. Only authorized and authenticated users should be allowed to access sensitive cloud-based data and applications. Securing the cloud is complex, but no more difficult than many of the security challenges that Vanguard has been solving for customers for more than 35 years.